A backdoor in Windows Remote Desktop Protocol allows logging in with old passwords after they have been changed. According to Microsoft, there is no problem.
A backdoor in Windows Remote Desktop Protocol (RDP) has the security world in an uproar. Researcher Daniel Wade discovered that RDP allows old passwords, even when they have already been changed by the account owner. The only one who sees no issue is Microsoft itself, which states it has no plans to close the backdoor.
read also
Windows Remote Desktop Protocol Allows Changed Passwords
Windows Remote Desktop Protocol allows remote login to a device and virtual takeover of control. This is useful for managed devices within companies, but not so convenient if an attacker possesses a password. With a valid RDP login, an attacker gains free rein over a device.
Old Passwords
If your password is compromised, your first reflex should be to change that password. But that does little good with Windows RDP, Wade discovered. The Windows Remote Desktop Protocol continues to accept old passwords, even when they have been changed by the account owner.
The backdoor is a result of how Remote Desktop Protocol stores passwords. The first time a user logs in, RDP will check the validity of the login credentials online. Once the green checkmark is given, Windows stores the credentials in an encrypted format locally on the device’s hard drive.
This means RDP doesn’t need to perform an online check every time. However, it also means that once a password is approved, RDP continues to approve it. The outdated password passes the check, causing security tools like Defender and Entra ID not to raise an alarm. On the contrary, the new password is more likely to be rejected because it doesn’t match the changed password.
Not a Backdoor, but a Feature
Although security experts see a major security risk in the backdoor, Microsoft is not worried at all. In a statement, Microsoft says Remote Desktop Protocol was intentionally programmed this way. Creating a local copy on the hard drive ensures that ‘at least one user can always log in’, the statement reads.
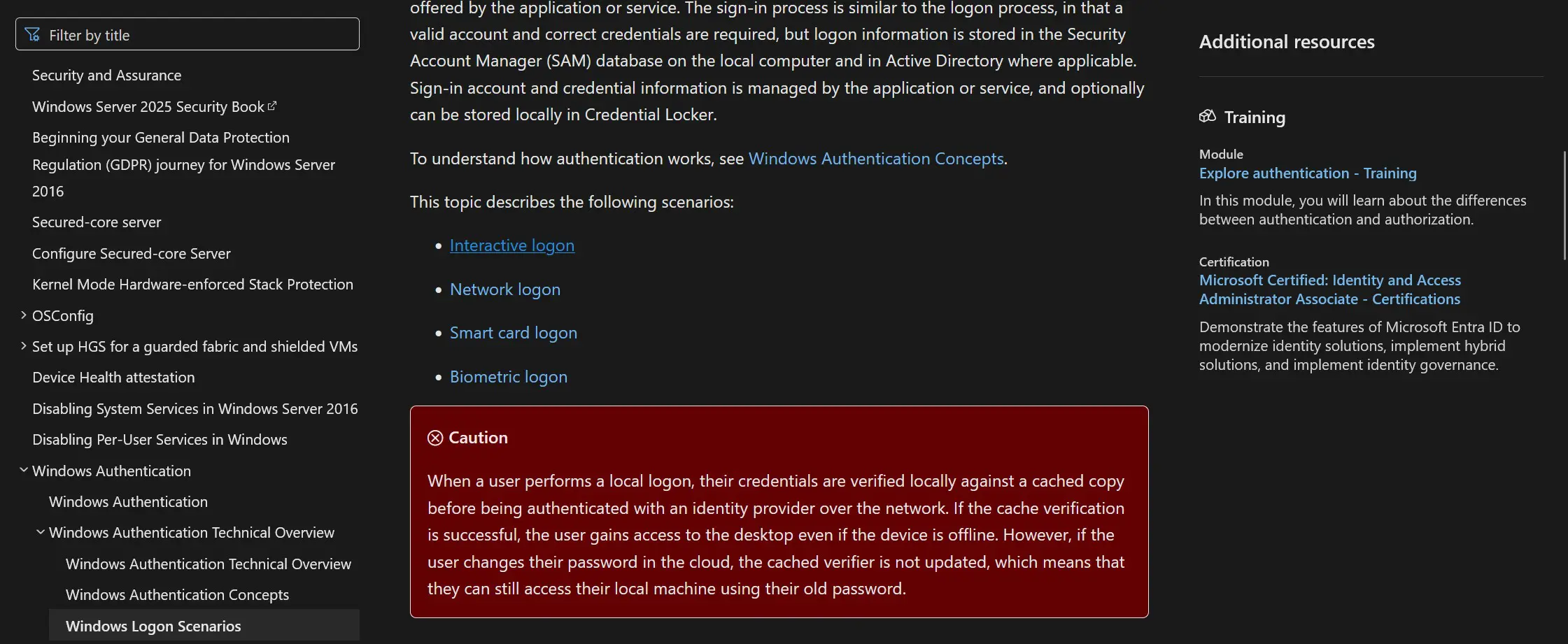
Microsoft therefore has no plans to modify the backdoor. The only action Microsoft is taking is placing a red warning on the information page of Windows login systems. In it, Microsoft states that ‘if the user changes their password in the cloud, however, the cached authentication is not updated, meaning they can still access their local computer with their old password’.
Windows Remote Desktop Protocol often causes problems. Especially during the coronavirus pandemic, it proved to be a popular gateway for remote cyberattacks. Microsoft’s nonchalant approach to potential backdoors in the system is met with incomprehension by security experts.
